https://medium.com/@z3roTrust/security-obscurity-9-19-compliance-security-ecf7a60d6ba9
If you’ve ever worked in the information security industry, then you’ve probably heard the old saying,
“Compliance Does NOT Equal Security!!!”
It’s true, you know. Attackers really don’t care if you’ve checked all the boxes on whatever checklist you’ve chosen or are required to adhere to a risk management framework (COBIT, NIST RMF, CIS Top 20, etc.). In fact, it is this author’s opinion that this particular saying bears repeating and it should probably be blasted from speakers throughout the greater Washington, D.C. area on a continuous loop where national policy and laws are created.
Here’s why: the government and many corporations continue to think that cybersecurity is all about compliance. They are lost beyond compliance, can’t think past it. Many such organizations are incredibly “fat,” as in they are large and they have enormous digital footprints in the number of Internet-connected systems they are responsible for. Due to this reason and the perceived shortage of qualified cybersecurity professionals, I’ve found that these organizations will often just do the bare minimum to get by even though many of these organizations can afford to do much better. They don’t consider it a wise business investment to fortify their cyber defenses and readiness.
This is the same logic someone might use when building a new home in a flood zone… It just doesn’t make sense. On the flip side, some organizations spend a fortune on state-of-the-art cybersecurity solutions and still end up getting pwned. This demonstrates that there is no easy, cut-and-paste solution to cybersecurity. It’s complicated and that is why security professionals get paid the big bucks to figure out and implement complex security solutions to difficult problems.
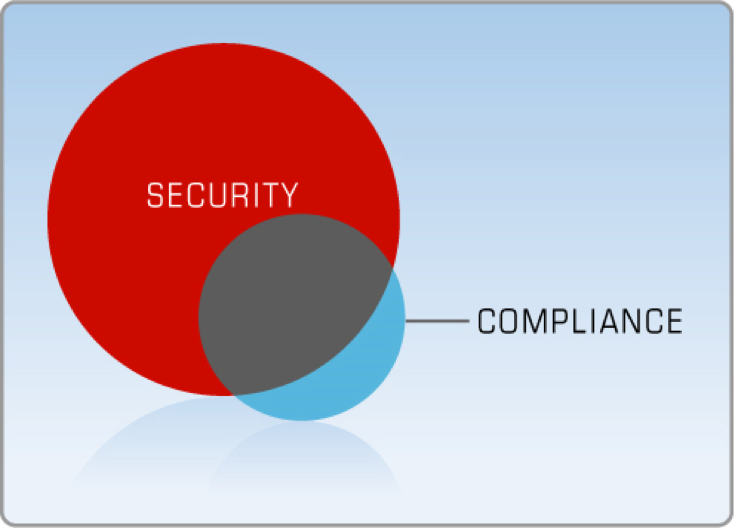
Regulatory compliance is only part of a robust security program.
**Pay Attention** It is not enough to simply check off boxes and write hundreds of pages of documentation about a system and then think you’re systems are secure.
This is one of the biggest reasons why American organizations continue to be hacked time and again by adversaries such as China and Russia. You’re making it too easy for the adversaries to compromise your networks. Yes, cybersecurity is expensive. Everyone knows that! But guess what’s even more expensive? Not having it… Go figure! Funny how that works, right? Get with the program and try actually giving a fuck about security.
Corporate Executives & Policy Wonks

As strange as though it may seem, there are those who work in cybersecurity that are nothing more than policy wonks and know next-to-nothing about the technical aspects of hardening and securing information systems. Now notice I used the term “cybersecurity” instead of information security (InfoSec) which usually denotes government or military flavor of information security. However, this astounding tidbit of information is not only prevalent in government and the Defense Industrial Base (DIB) that supports the government, but it is also rampant in corporate America. As throughout history, we have people with no technical background or that haven’t worked in a technical capacity in a very long time that are making critical security decisions. It’s a recipe for disaster and needs to change. This is a form of security through obscurity because these organizations think they are doing it correctly when they are failing miserably.
Companies That Passed Audits But Still Got Hacked

Let’s take the recent example of Target, for example. Target successfully passed a Trustwave audit for compliance with the Payment Card Industry Data Security Standard (PCI DSS) before being hacked and suffering a monstrous data breach in 2013 that compromised 70 million customers’ Personally Identifiable Information (PII) and 40 million customers’ credit card numbers (Lacy & de Metz, 2014). Any retailer that processes credit card transactions is required to comply with the PCI DSS. Trustwave was sued by Trustmark National Bank and Green Bank as a result. Oh, what a tangled web we weave.
Attackers not only breached the network but were actively exploiting the network for “nearly three weeks on Trustwave’s watch before it was detected by third parties and reported to Target” (Schwartz, 2014). Target had outsourced network intrusion monitoring services to Trustwave as a Managed Security Service Provider (MSSP).
This case is a classic example of how being compliant does not guarantee security.
One also has to wonder if Target completed the online questionnaire for Trustwave PCI DSS compliance audit or if it was done by actual Trustwave auditors, in-person on-premise? If the audit was self-administered by answering an online questionnaire, then Target likely failed to answer the questions truthfully or accurately whether intentionally or as a result of technical incompetence on the part of their CIO/CISO. Either way, it demonstrates the fallacy of compliance equaling security which is something that government, corporations, organizations, and security professionals should always be on the lookout for. Is what you are doing, all that compliance artifact documentation, really helping to secure your systems is it, in fact, affecting your ability to harden and protect them?
Cybersecurity is a Myth
Cybersecurity is a myth? Well, ok. Fair enough, not exactly but sometimes it sure seems that way these days in the era of the data breach. There are certain steps that you and organizations can take to harden systems that will help protect them from compromise. However, the ages-old problem with computers and networks, in particular, remains and always has been that there are so many different attack vectors and surfaces that it is nearly impossible to defend.
Each port out of 65,535 TCP and another 65,535 UDP ports (131,070 total entry ports) could be compromised if not properly closed by a firewall and which have to be monitored, each program application (browsers, Microsoft Office, Adobe, etc.) can also be compromised, and then there are operating systems and Internet protocols that can also be hacked. Oh, and let’s not forget emails with malicious links or the malicious links found on many websites that can also lead to compromise. Users present the greatest risk of all, but surprisingly many organizations do not require mandatory cybersecurity training for its employees. The odds are against remaining breach-free.
In fact, it has been said that “There are only two types of companies in this world, those who know they’ve been hacked and those who don’t.”
This saying is spot on. The attackers are extremely motivated to hack into companies if they are large and rich in either information or money. Attackers only need to get lucky once to get inside your system whereas the cybersecurity defenders have to be right every single time, 24/7/366 days on a Leap year. Those are not very good odds if you’re a betting man. In fact, it’s practically a mission impossible movie plot.
The cybersecurity industry has many skilled and knowledgeable cybersecurity professionals, but when you hire them and tell them they’re responsible for 75 different systems of various sizes and architectures, software baselines, OS types, the job of defending that many different computers and network components becomes not only a daunting task but flat-out impossible. Merely updating software patches alone on that many systems or Local Area Networks (LANs) is challenging as often as new patches are released by software vendors and with competing demands that security professionals have to contend with not to mention not being able to temporarily bring down production systems that will affect business operations. Then there are firmware updates for networking hardware components, security scans, system event log reviews, and the list goes on and on.
It is a tall order to protect networks, especially if the organization spreads its cybersecurity workforce too thin, leadership doesn’t back them up, doesn’t give them the budget they need to hire enough qualified employees and implement security controls and tools, or doesn’t give them a seat at the decisionmaker table. Perhaps the analogy of a dog attempting to fight off a pack of wolves better reflects the situation here. The dog will try valiantly to defend himself or his master or territory, but in the end, the dog will be ripped to pieces by the wolves. Except in this analogy, the dog is the lone cybersecurity professional who is battling against armies of hackers, even Advanced Persistent Threat (APT) groups, at that! He/she doesn’t stand a chance folks, no matter how good they are. The odds are stacked against success. Again, this is a form of security through obscurity. It’s delusional.
In fact, I’ll even go as far as to say that the whole concept of paying for a half-assed cybersecurity workforce and program while doing the bare minimum to meet regulatory compliance and purchasing the minimum amount of security tools is by definition, “security through obscurity.” It’s a scapegoat plan for corporate execs so that when there is a data breach, because we all know there will be, the corporate executive goons can point to the fact that they’ve spent hundreds of thousands or millions of dollars on cybersecurity, they follow the NIST Cyber Security Framework (CSF), and they still got hacked! Well, of course, they did. They’re doing the bare minimum…
Therefore, they will point their fingers at the CISO and their team of security professionals (i.e., if they even paid to have a team of security professionals, let alone hire a CISO). It must be the security team’s fault!! Fire them all! Alas, what are these poor schmucks supposed to do, right? Cry me a river! I have zero pity for this foolishness and these organizations like Equifax, Citibank, or any number of other recent examples. If you find yourself working for an organization like this in a cybersecurity professional capacity, you might consider seeking employment elsewhere. Then officials cry foul that other nations like China, Russia, North Korea, or Iran are stealing intellectual property (IP) and billions in Research & Development (R&D) via Computer Network Espionage (CNE). Well, how is it that they’re able to do that?
Fools, the important data should never have been connected to the Internet, let alone the Cloud, in the first place! In their haste to outsource everything to the Cloud and save millions in IT infrastructure and manpower resources, they failed to think about the long-term implications of security in the Cloud and the increasing costs of Cloud services. What seemed to be cheap and so much better at first will not stay that way. Wait until it’s time to renew that contract and did your legal team scrub the fine print on the Service Legal Agreement (SLA)? What’s that? There was no SLA? Have fun with that one…
What Else Can We Do Beyond Compliance Checks?
There is so much more to cybersecurity than just doing the bare minimum and following best practices that are part of a risk management framework. Even with a robust compliance framework like the NIST Risk Management Framework (RMF), there is still room for improvement by any organization that implements it. Do you honestly think that implementing the CIS Top 20 controls is going to fully protect your systems? Do you as a security professional truly believe that? Sure, it is better than most organizations will do, but surely there are improvements that you can add, right? It is not enough to mature a system’s security level to the point where it meets compliance and then abandon it after it is authorized for production. You have to nurture that system like a plant, feed it software updates and refined system configuration settings, monitor it, report on it’s progress to authorizing officials. It’s not just about meeting minimum compliance thresholds and then turning our attention elsewhere to other projects. As long as those systems are powered on, connected to the Internet, and processing information, they should and need to be continuously monitored and updated. In the NIST RMF this is known as Step 6, Continuous Monitoring. Something that hardly anyone follows correctly.
I have to believe that security professionals are either having their hands tied by their organizational leadership or are completely incompetent whenever I encounter a situation where they’re only doing the bare minimum to achieve compliance. Why even bother? That’s what I ought to say, but I don’t. Instead, they usually fail an assessment even though they are contractually required to comply with “X” number of regulatory compliance laws. Stiff penalties for not passing an assessment and not complying with cybersecurity requirements are still not really a thing yet. Rather than call them out on their BS cybersecurity strategies we’d rather be politically correct and them give them goals to get “healthy.” Here’s another chance to fix your deficiencies, we’ll be back in a couple of months to check up on how you’re doing. Meanwhile, the hackers are having a field day on your networks…
Instead of tailoring out security controls that “don’t apply” for whatever reason, perhaps you should spend the time and money on implementing all of the controls that are practically feasible without hampering your business operations ability. Adversaries want you to take shortcuts in your security implementation, so yeah! Maybe shortcuts are not the answer… Just a thought. Don’t make the job of the cybercriminal easier by employing security through obscurity!